CogniSoc
From Security Operations Centers to BioNeuroCognitive Reasoning Systems
The traditional Security Operations Center was built for a simpler cyber world.
It was designed to collect signals, monitor alerts, investigate incidents, escalate problems, and coordinate technical responses. For a long time, that model was sufficient. It was never perfect, but it worked reasonably well when cyber threats were more linear, infrastructures were less fragmented, and the operational tempo of attacks was slower.
That world has disappeared.
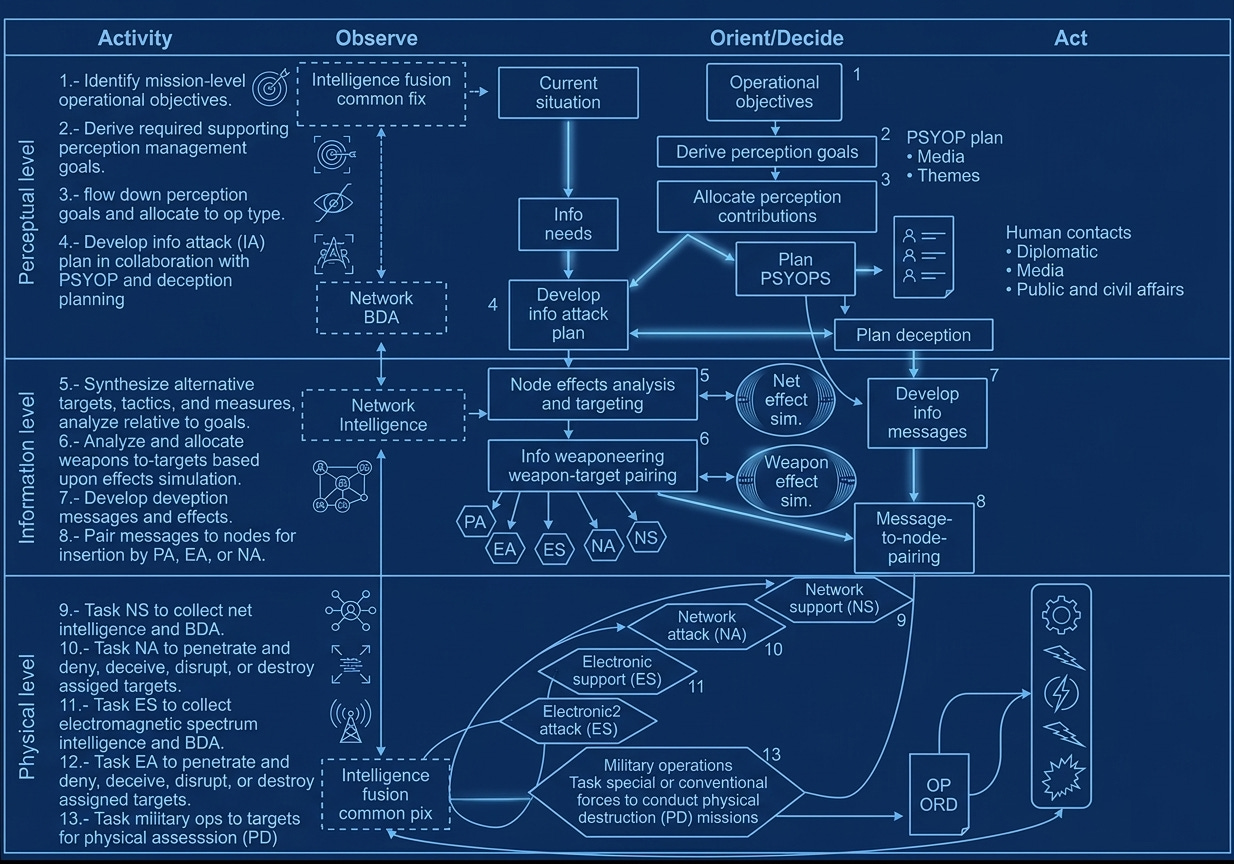
Today’s SOC must operate inside a threat landscape shaped by cyber espionage, cyber terrorism, cybercrime, hybrid conflict, information warfare, and state-sponsored operations. The adversary is no longer only trying to penetrate a network. It may be trying to persist silently, manipulate information, poison decision-making, degrade trust, compromise supply chains, or prepare strategic effects long before the visible attack begins.
This changes the nature of cyber defence.
The modern SOC can no longer be understood merely as a monitoring room, a collection of tools, or a reactive incident-response function.
It must become a cognitive defence system.
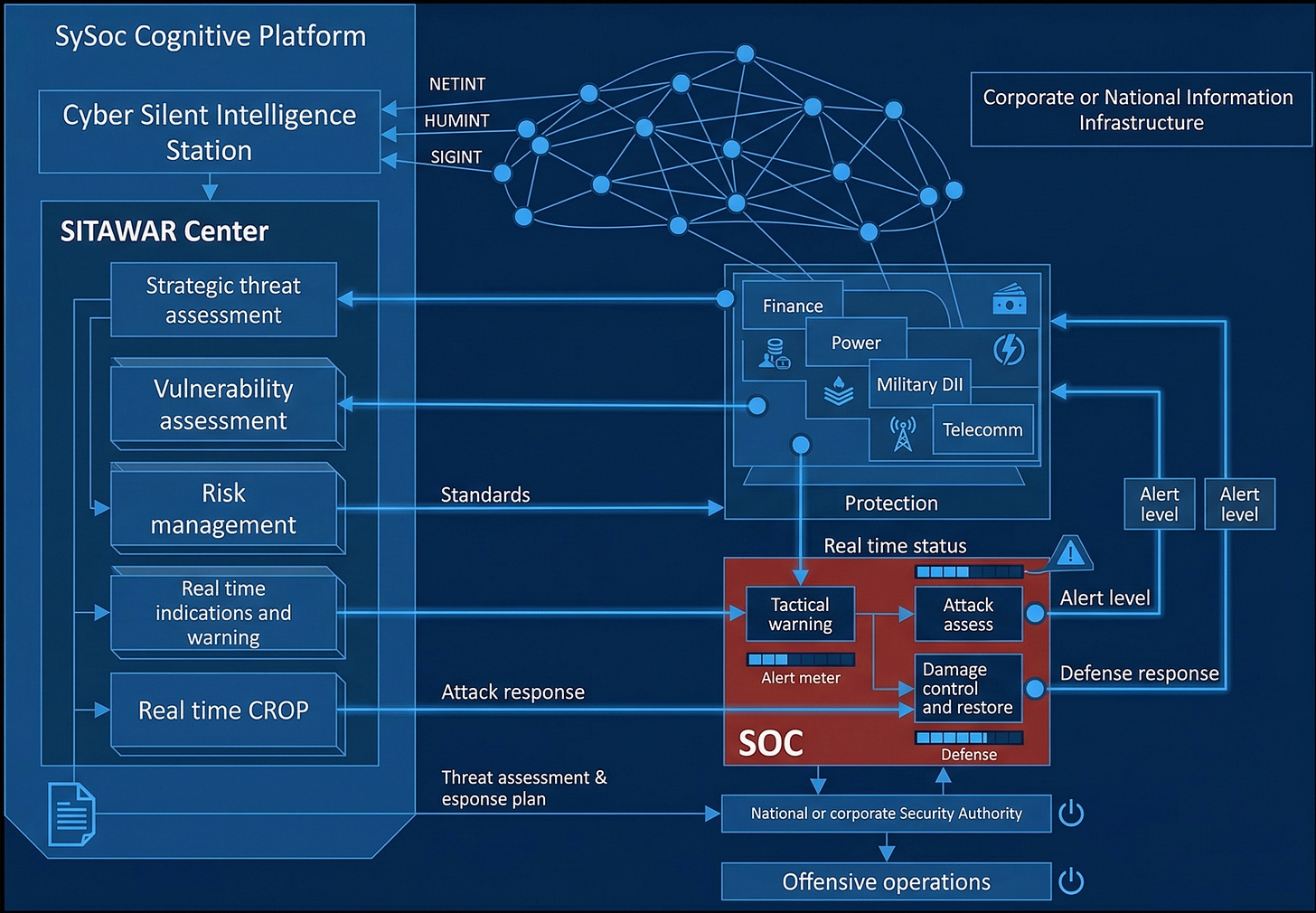
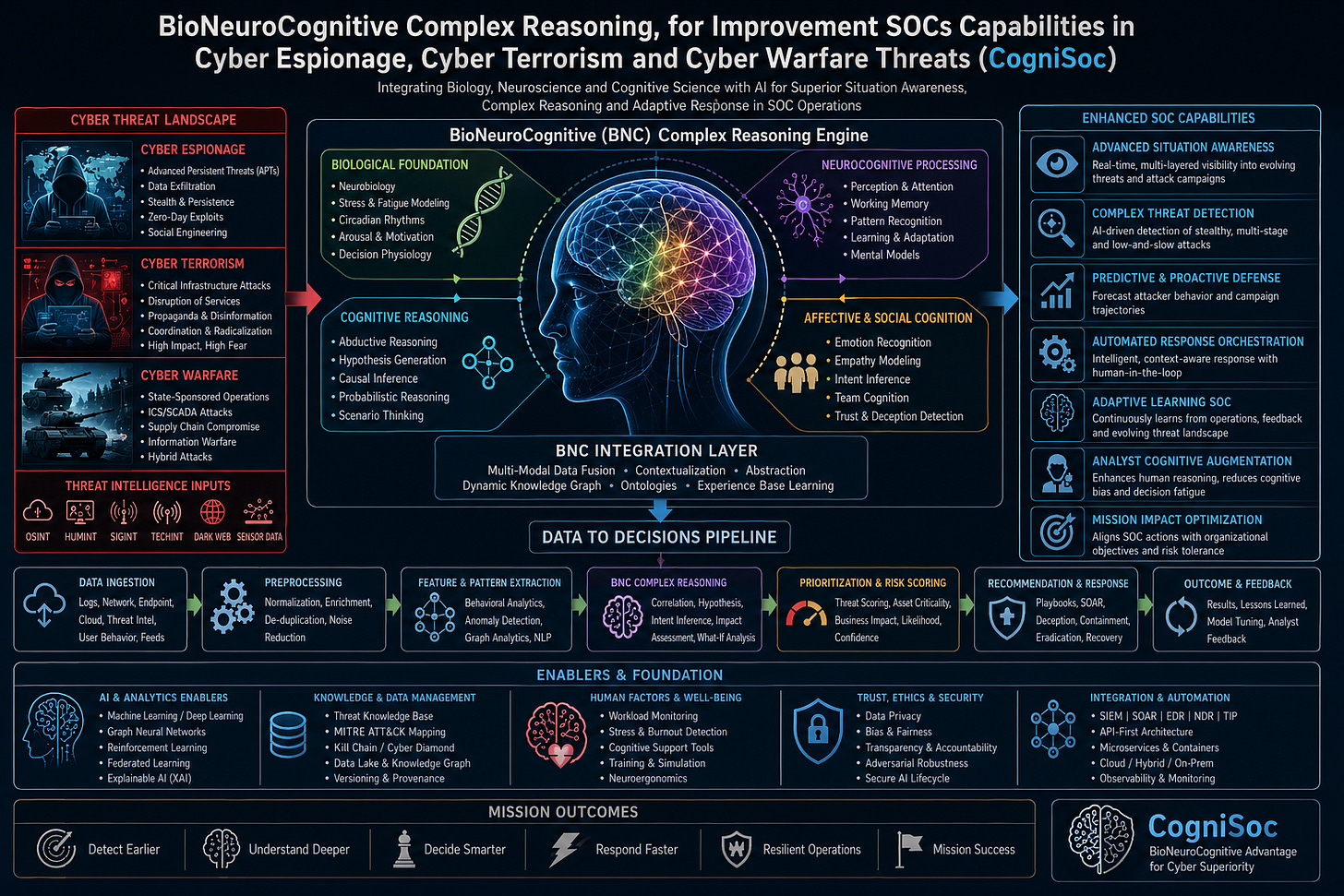
That is the central idea behind CogniSoc, a BioNeuroCognitive approach to improving SOC capabilities in cyber espionage, cyber terrorism, and cyber warfare scenarios.
The limits of the traditional SOC
Most current SOCs suffer from a structural mismatch.
They are expected to defend against highly adaptive adversaries, but they are often organized around static processes, fragmented technologies, and human operators under severe cognitive overload.
The first deficiency is doctrinal.
Many SOCs lack an advanced operational model that allows them to scale their capabilities from low-complexity threats, such as hacktivism or opportunistic intrusion, to sophisticated campaigns involving advanced persistent threats, cyber espionage, deception operations, critical infrastructure attacks, and cyber warfare.
This produces a dangerous flatness.
The SOC treats very different threat types as if they were only different levels of severity. But hacktivism, ransomware, espionage, sabotage, cyber terrorism, and state-sponsored warfare do not follow the same logic. They differ in intent, tempo, persistence, operational design, political meaning, and strategic consequence.
A mature SOC must therefore reason across levels of complexity.
It must detect simple attacks quickly, but it must also identify slow, silent, and indirect operations that may not trigger conventional alarms.
It must distinguish noise from deception.
It must understand whether an event is isolated, coordinated, preparatory, or part of a wider adversarial campaign.
That requires more than detection.
It requires doctrine, cognition, and reasoning.
Cognitive overload as a security vulnerability
The second major weakness is cognitive overload.
SOC operators and managers are increasingly exposed to volumes of information that exceed human decision-making capacity:
Too many alerts.
Too many dashboards.
Too many vendors.
Too many partial indicators.
Too many dependencies between networks, endpoints, cloud environments, users, identities, business processes, suppliers, and mission-critical systems.
The result is not only fatigue. It is operational paralysis.
When a SOC lacks ultra-early multidimensional situational awareness in critical real time, decision-making becomes slower, more fragile, and less reliable precisely when speed and judgement matter most.
Cyber defence is time-sensitive. The useful window for anticipation, containment, attribution, response, and consequence management can be extremely narrow. A delayed decision may allow lateral movement, privilege escalation, data exfiltration, information manipulation, operational disruption, or strategic escalation.
The next-generation SOC must therefore reduce cognitive load instead of adding to it.
It must help humans see earlier, understand faster, reason better, and act with greater precision.
Fragmented architectures create fragmented understanding
A third weakness lies in the architecture of current cyber defence environments.
Many SOCs operate across complex ecosystems composed of products from different manufacturers, each with its own interface, data model, detection logic, telemetry format, and administrative requirements.
This creates operational inefficiency.
More importantly, it creates fragmented understanding.
When data is distributed across disconnected systems, when context is lost between tools, and when analysts must manually reconstruct the meaning of events, the SOC becomes reactive. It may see thousands of signals, but still fail to understand the situation.
Sophisticated adversaries exploit precisely these gaps.
They attack seams, transitions, dependencies, trust relationships, identity systems, supply chains, and organizational blind spots.
The problem is not only whether the SOC has enough tools.
The problem is whether those tools can be composed into a coherent reasoning environment.
AI without doctrine is not enough
Most organizations now understand that AI will be important for cybersecurity.
Fewer organizations have a clear doctrine for where and how AI should be applied inside the SOC.
This distinction matters.
AI can filter alerts, correlate evidence, prioritize incidents, detect anomalies, recommend actions, generate hypotheses, support threat intelligence, orchestrate responses, and even make autonomous decisions in critical real time.
But these functions are not equivalent:
Some should augment human analysts.
Some should advise SOC managers.
Some may be delegated to autonomous systems under strict constraints.
Some must remain under human authority.
The strategic question is not whether AI should be used. The question is where AI should assist, where it should advise, where it should decide, and where it must remain subordinated to human command.
Without that distinction, AI becomes either cosmetic or dangerous.
Cosmetic AI adds automation without changing the cognitive architecture of the SOC.
Dangerous AI acts without sufficient explainability, accountability, doctrine, or control.
CogniSoc proposes a different path. AI should not merely automate SOC tasks. It should become part of a structured reasoning architecture that connects machines, analysts, managers, procedures, evidence, risk, and mission objectives.
Why BioNeuroCognitive AI matters
BioNeuroCognitive AI offers a useful conceptual foundation because it does not treat intelligence as a single mechanism.
It integrates lessons from biology, neuroscience, and cognitive science into AI systems designed for adaptive reasoning, situational awareness, complex decision-making, and coordinated response.
In the context of cyber defence, this matters because a SOC is not only a technical platform. It is a living socio-technical system.
It must perceive.
It must attend.
It must remember.
It must recognize patterns.
It must generate hypotheses.
It must learn from experience.
It must manage uncertainty.
It must coordinate action.
It must adapt to changing environments.
A BioNeuroCognitive SOC would therefore be built around a complex reasoning engine rather than around alert processing alone.
This reasoning engine would integrate biological inspiration, neurocognitive processing, cognitive reasoning, affective and social cognition, multimodal data fusion, ontologies, dynamic knowledge graphs, and experience-based learning.
The objective is not to imitate the brain superficially.
The objective is to build a cyber defence architecture capable of adaptive cognition.
From data to decisions
The core transformation is the movement from data ingestion to reasoned decision.
A traditional SOC often begins with logs, network data, endpoint telemetry, cloud signals, user behavior, threat intelligence, and external feeds. These inputs are then normalized, enriched, deduplicated, and processed through detection systems.
That pipeline is necessary.
But it is not sufficient.
CogniSoc extends this pipeline into a reasoning process.
First, data is ingested from heterogeneous sources.
Then it is preprocessed and contextualized.
Then features and patterns are extracted through behavioral analytics, anomaly detection, graph analytics, and natural language processing.
Then BioNeuroCognitive reasoning begins.
This reasoning layer correlates evidence, generates hypotheses, infers intent, assesses mission impact, and asks what-if questions.
After that, the system prioritizes risk according to threat score, asset criticality, business impact, likelihood, and confidence.
Finally, it recommends or orchestrates responses through playbooks, containment, deception, eradication, recovery, and feedback loops.
This is the difference between a SOC that receives information and a SOC that thinks operationally.
Enhanced SOC capabilities
A BioNeuroCognitive SOC would improve several decisive capabilities.
It would provide advanced situational awareness. Not only visibility into isolated events, but real-time, multi-layer visibility into evolving threats and attack campaigns.
It would enable complex threat detection. This means identifying stealthy, multi-stage, and low-and-slow attacks that conventional detection systems may miss.
It would support predictive and proactive defence by forecasting attacker behavior and possible campaign trajectories.
It would improve automated response orchestration. Not blind automation, but intelligent, context-aware response with a human-in-the-loop where required.
It would create an adaptive learning SOC. The system would learn continuously from operations, feedback, analyst judgement, new threats, organizational change, and the evolving threat landscape.
It would augment human analysts. The purpose is not to replace human reasoning, but to reduce cognitive bias, decision fatigue, and information overload.
It would optimize mission impact. SOC actions would be aligned not only with technical severity, but with organizational objectives, business risk, operational continuity, and strategic tolerance.
This is a crucial shift.
The SOC should not only ask what is technically compromised.
It must ask what matters.
Silent attacks and deception operations
One of the most important applications of complex reasoning is the detection of silent attacks.
Many advanced operations do not begin with noise. They begin with patience.
The adversary may persist quietly, map the environment, test access, manipulate identity systems, alter data, observe workflows, or introduce false information into corporate systems.
These operations may not look like classic attacks.
They may look like normal activity.
That is why simple detection is insufficient.
CogniSoc must reason about behavior, context, intent, anomaly, deception, and consequence.
This is especially important in operations aimed at manipulating information. In such cases, the SOC is not only protecting confidentiality, integrity, and availability. It is protecting the epistemic integrity of the organization.
What does the organization believe to be true?
Which data can it trust?
Which decision processes depend on manipulated information?
Which systems may have been poisoned without being visibly disrupted?
This is where cyber defence becomes cognitive security.
The foundations of CogniSoc
A BioNeuroCognitive SOC requires several foundational layers.
It needs advanced AI and analytics, including machine learning, deep learning, graph neural networks, reinforcement learning, federated learning, and explainable AI.
It needs knowledge and data management, including threat knowledge bases, MITRE ATT&CK mapping, kill chain modelling, cyber diamond models, data lakes, knowledge graphs, versioning, and provenance.
It needs attention to human factors and well-being, including workload monitoring, stress and burnout detection, cognitive support tools, training, simulation, and neuroergonomics.
It needs trust, ethics, and security, including data privacy, bias control, transparency, accountability, adversarial robustness, and secure AI lifecycle management.
And it needs integration and automation, including SIEM, SOAR, EDR, NDR, threat intelligence platforms, API-first architecture, microservices, cloud, hybrid and on-prem environments, observability, and monitoring.
This is not a single tool.
It is an ecosystem.
Mission outcomes
The objective of CogniSoc is not technological sophistication for its own sake.
The objective is mission advantage.
A BioNeuroCognitive SOC should detect earlier.
Understand deeper.
Decide smarter.
Respond faster.
Operate more resiliently.
And increase the probability of mission success under adversarial pressure.
This is the real measure of a next-generation SOC.
Not the number of alerts processed.
Not the number of dashboards displayed.
Not the number of tools integrated.
The measure is whether the organization becomes cognitively stronger in the face of complex cyber threats.
The SOC must learn to reason
Cyber espionage, cyber terrorism, and cyber warfare will not be defeated by more alerts alone.
Nor by more fragmented tools.
Nor by automation without doctrine.
The decisive advantage will belong to the defenders who can reason faster, deeper, and more coherently than the adversary.
That requires a new model of the SOC:
A model based on ultra-early situational awareness.
A model based on adaptive learning.
A model based on complex reasoning.
A model based on the intelligent coordination of systems, people, procedures, and mission objectives.
That is the promise of CogniSoc.
The next-generation SOC will not simply monitor the cyber battlefield.
It will think within it.